When you hear "oracle" in blockchain, you might think of decentralized data feeds that connect smart contracts to real-world information. But in enterprise software, Oracle is a company - and its systems are some of the most targeted in the world. The recent CVE-2025-61882 vulnerability didn’t just expose a bug. It exposed how deeply embedded, high-value enterprise systems can become attack surfaces for criminals - and how easily they can be manipulated, even without a password.
What CVE-2025-61882 Actually Means
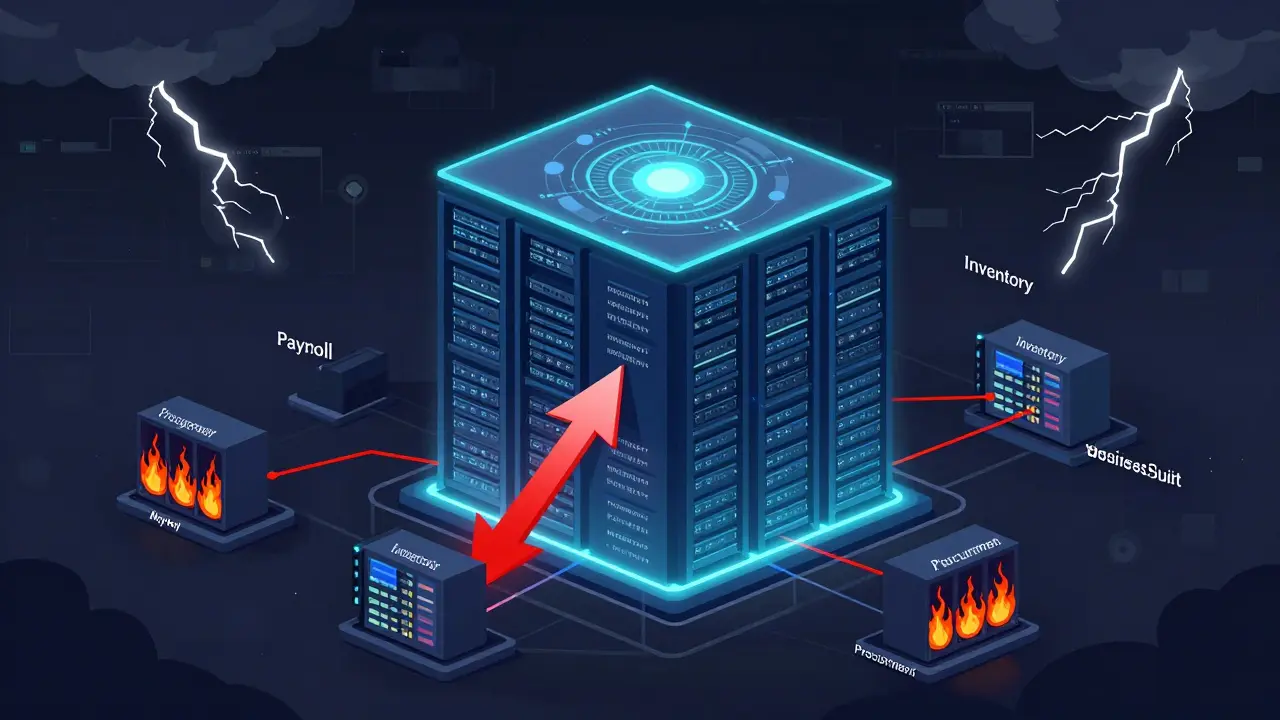
On October 4, 2025, Oracle dropped an emergency security alert. Not the kind you get every few months. This was a Saturday night alert - the kind that wakes up IT teams at 2 a.m. The vulnerability, CVE-2025-61882, affected Oracle E-Business Suite versions 12.2.3 through 12.2.14. And here’s the scary part: attackers didn’t need a username or password to exploit it. Just network access. That’s it. No login. No phishing. No social engineering. Just a single HTTP request from anywhere on the internet. This wasn’t a simple buffer overflow. Security researchers at WatchTowr Labs found it was a chain of five separate bugs working together. Each one alone wouldn’t do much. But strung together? They let attackers take full control of systems running Oracle’s core business software. Think payroll, inventory, procurement - all the systems that keep Fortune 500 companies running. Once inside, attackers could steal data, delete records, or install ransomware. The fact that this exploit was already being used in real-world data extortion attacks before Oracle even disclosed it tells you something important: someone had this weapon for weeks, maybe months, and was quietly testing it on live systems.Why Oracle Systems Are Prime Targets
Oracle doesn’t just sell software. It sells the backbone of global business. Over 80% of Fortune 500 companies use Oracle E-Business Suite. Governments, banks, hospitals - they all rely on it. That makes it a goldmine for attackers. A single breach can mean access to payroll data, supplier contracts, financial reports, and customer records - all in one system. What makes it worse is how Oracle’s software is built. It’s not one app. It’s dozens of interconnected pieces: database, middleware, application servers, reporting tools, and more. A flaw in one component can open doors to others. In 2025 alone, Oracle released patches for 9 vulnerabilities in E-Business Suite, with 3 of them exploitable without authentication. The April update fixed two more in Oracle TimesTen - again, no login needed. Five out of six patches for Oracle Commerce were also remotely exploitable without credentials. This isn’t random. It’s a pattern. Oracle’s architecture, designed for integration and scale, creates blind spots. Authentication checks are often skipped between internal services for performance. Attackers exploit those trust relationships. They don’t need to break in. They just need to slip through the back door.How This Relates to Blockchain Oracles
You might be wondering: how does this connect to blockchain? Because blockchain oracles - the services that feed real-world data like stock prices or weather into smart contracts - face the same core problem: trust. If a blockchain oracle gets hacked, the whole smart contract can be manipulated. A fake price feed could trigger a loan repayment, drain a DeFi pool, or crash a token. The Oracle E-Business Suite breach shows what happens when a centralized data source is both critical and poorly secured. In blockchain, decentralized oracles are supposed to solve this. But if you’re using a single provider - even if it’s labeled "decentralized" - you’re still vulnerable. The lesson from CVE-2025-61882 is simple: centralized data, no matter how big the brand, is a single point of failure. Companies using blockchain oracles should take note. Relying on one vendor for price feeds? That’s like running Oracle E-Business Suite without a firewall. The best blockchain oracles use multiple sources, cross-validate data, and have built-in anomaly detection. If you’re not doing that, you’re not secure - you’re just hoping.
Real-World Impact: Data Extortion in Action
CRN reported that Oracle confirmed a direct link between CVE-2025-61882 and active data extortion campaigns. Attackers didn’t just steal data. They encrypted it, demanded ransom, and threatened to leak financial records to regulators or competitors. One manufacturer lost three weeks of production planning. A logistics firm had its entire shipment tracking system wiped. The cost? Not just in ransom. It was in downtime, lost contracts, and reputational damage. What made these attacks so effective? The attackers didn’t need to guess passwords or trick employees. They targeted the system’s weakest link: the assumption that internal services were safe because they weren’t directly exposed. But in reality, many Oracle E-Business Suite instances were sitting on the internet - unpatched, unmaintained, forgotten. This is the hidden risk of enterprise software: it’s often deployed once and never revisited. Systems get moved to the cloud, merged, upgraded - but security checks lag. By the time someone notices a vulnerability, it’s already too late.What You Can Do to Protect Your Systems
If you’re using Oracle E-Business Suite or any enterprise software, here’s what you need to do right now:- Inventory every Oracle instance. Don’t assume you know where they all are. Use network scans. Check cloud logs. Find every server running versions 12.2.3 to 12.2.14.
- Apply the patch immediately. Oracle released a patch on October 5, 2025. If you haven’t installed it, you’re still exposed.
- Isolate internet-facing systems. If Oracle E-Business Suite doesn’t need to be public, block it. Use network segmentation. Don’t let one server be the gateway to your entire operation.
- Monitor for exploitation signs. Look for unusual HTTP requests to /servlet/ICX* paths. Watch for new processes named "fndcpesr" or "FNDCPAPR" spawning unexpectedly. These are known indicators of the exploit.
- Don’t wait for the next patch. The next critical vulnerability is already being discovered. Assume it will be exploited before it’s patched.


21 Responses
So this CVE-2025-61882 isn't just another patch day headache-it's a wake-up call that we've been treating enterprise software like it's invincible. I've seen orgs run Oracle EBS on public IPs for years because 'it's always been fine.' Turns out, 'fine' is just a temporary state. The fact that attackers were testing this before disclosure? That's not luck. That's systemic neglect. We need to stop assuming vendors have our back. They're building for scale, not security. And honestly? We're the ones who have to clean up the mess.
OMG this is SCARY 😱 I just read this and my heart dropped. Like… what if this was MY company? Imagine payroll just GONE. Or inventory disappearing. We’re all just one unpatched server away from chaos. Please, please, please patch your systems. I’m begging you. Don’t wait. Just do it. 💪
From an architectural standpoint, this exploit chain is a textbook case of trust boundary erosion across Oracle’s middleware stack. The lack of service-to-service authn between ICX servlets and backend EBS modules creates a lateral movement vector that’s practically a gift to threat actors. The real takeaway? Legacy integration patterns built for performance over zero-trust are now liability multipliers. We need to refactor our SOA landscapes, not just patch CVEs.
Y’all need to stop panicking and start planning. This is why we do quarterly asset inventories and automated patch workflows. 🤝 I’ve got a script that scans our cloud environment every Sunday for unpatched Oracle instances. If you don’t have one, DM me-I’ll share it. We’re all in this together. No one’s getting left behind. 💪
man i just found 3 oracle ebs boxes on our network that we forgot about. like… they were moved to azure but nobody updated the firewall rules. this post is a slap in the face. we’re patching tonight. thanks for the heads up. 🤦♂️
Oh wow. Another ‘trusted vendor’ failure. How revolutionary. Let me guess-this is the same company that told us their cloud was ‘air-gapped’ while storing customer data on public S3 buckets? You know what’s funny? The same people who built this mess are now writing whitepapers about ‘zero trust.’ Pathetic. If you’re still using Oracle EBS without a full rewrite, you’re not secure-you’re just gambling.
Let’s be real-this isn’t about Oracle. It’s about incompetent IT departments that treat security like a checkbox. I’ve seen companies ignore patches for 18 months because ‘it’s not in budget.’ Then they wonder why ransomware hits. You don’t get to be lazy and then cry when you get hacked. This is 100% on the orgs. Not the vendor. Fix your house before blaming the architecture.
It’s ironic that we’re discussing blockchain oracles while ignoring the fact that enterprise software itself operates as a centralized oracle with no verification layer. The parallels are not coincidental. Both rely on blind trust in a single source. The difference? One is intentionally decentralized; the other is accidentally, dangerously centralized. The solution isn’t more patches-it’s architectural rethinking.
in india we have so many small factories still running oracle 12.2.3 on windows xp machines. literally. no one even knows what a patch is. this is why cyberattacks are global. it’s not just the big corps. it’s the forgotten systems. we need outreach, not just alerts.
If you’re running Oracle E-Business Suite, you need a runbook. Not a checklist. A runbook. Step-by-step: scan, isolate, patch, validate, monitor. I’ve helped 12 companies through this exact exploit. The ones that survived? They had a plan. The ones that didn’t? They’re still explaining to auditors why their inventory data vanished. Don’t be them.
This isn’t a vulnerability. It’s a coroner’s report for enterprise software’s outdated corpse. Oracle built a Frankenstein’s monster of interconnected modules, slapped a ‘secure’ sticker on it, and called it a platform. Now we’re all picking up the pieces. And for what? To save $2 million on licensing? We’re not paying for security-we’re paying for the illusion of it.
There is no excuse. None. Zero. The patch was released on October 5, 2025. If you haven’t applied it, you are not a victim-you are negligent. You are the reason these attacks succeed. You are the reason companies lose data. You are the reason trust in enterprise systems is eroding. Stop hiding behind ‘we’re waiting for testing.’ That’s not a reason. It’s a cowardice.
It is imperative to emphasize that the multi-stage exploit chain of CVE-2025-61882 underscores the criticality of defense-in-depth strategies. Each vulnerability exploited-though individually non-critical-collectively enabled full system compromise. Therefore, it is recommended that organizations implement network segmentation, application-layer firewalls, and behavioral anomaly detection to mitigate such layered threats. Proactive monitoring is not optional-it is foundational.
patching? nah. we’re moving to SAP. and guess what? SAP’s got the same damn issues. you think this is unique? it’s not. it’s the whole damn industry. if you’re not building your own data feeds from scratch, you’re just borrowing trouble. stop outsourcing your security. build. or get out.
Trust is not a system. Verification is.
my team just found 2 unpatched servers we didn’t even know existed. i’m so glad this post came out. we’ve been so focused on new projects we forgot about the old ones. we’re patching tonight. thank you for the reminder.
wait so if oracle is the problem… why are we still using it? i mean… like… if your car has a known brake flaw and the manufacturer says ‘oh just drive slower’… do you keep driving? no. you get a new car. why are we still clinging to this?
i’ve been in this game 20 years. this isn’t the first time we’ve seen this. it’s the 17th. same pattern: big vendor, complex system, ignored patches, silent exploitation. the only difference now? we have blockchain oracles doing the same thing. the lesson? don’t trust. verify. repeat. always.
thank you for writing this. i was about to ignore this patch. now i’m not. you made me think. seriously. i’m patching tonight. and i’m telling my team. you saved us.
you’re all missing the point. this isn’t about Oracle. it’s about how we worship tech giants. we act like they’re infallible. we don’t audit. we don’t question. we just pay and pray. blockchain oracles? same delusion. the real vulnerability isn’t in the code-it’s in our mindset. fix that first.
my company patched this within 48 hours. we use automated scanning + slack alerts. it’s not hard. it’s just not sexy. but hey-if you don’t care about your payroll data, that’s on you. 🙃